Restricting SFTP Access
By: Stuart Arnett | Principal Architect
SFTP provides a mechanism to authenticate and transfer files securely between servers. It also allows authentication using SSH keys instead of username and password authentication. Using SSH keys is considered a better security practice for authentication because they are more difficult to hack with brute force. SFTP also simplifies firewall and network configuration because it only requires a single port to be opened to access the server.
Using SFTP on a server does have some security concerns:
- – The out-of-the-box configuration when setting up a Linux server allows users to access the server both via SSH and SFTP.
- – Individuals using SFTP have access to system files that could be a security concern. (ex., /etc/passwd).
- – Users could access files uploaded by other users if the correct folder/file system permissions are not specified when uploading files.
This tutorial will walk you through how to set up a Linux server to provide the following functionality:
- – Restrict which users can SSH into the server and which users can only access the server using SFTP.
- – Restrict the SFTP users to a specific folder and sub-folders, eliminating the possibility of accessing files they shouldn’t see.
- – Configure the permissions required for an admin user to have access to all the files uploaded via SFTP users and be able to share files with the SFTP users which can then be downloaded.
Setting Up the Demo Environment
We will be using the following for setting up the demo:
- Operating System: Amazon Linux 2
- SFTP Server: OpenSSH Secure Shell Daemon (SSHD)
Group Setup
A new group will need to be added to the server to allow admin user(s) to access the files uploaded by any of the SFTP users and to allow admin user(s) to add files to the SFTP user’s download folders.
groupadd sftp-admin
User Account Setup
We will add three users to the server:
- – sftpadmin – Admin user with access to all the files uploaded by the SFTP users with the ability to also add files to the SFTP users’ download folders. The sftpadmin user won’t be able to access the server using SSH or SFTP, but the account can be accessed using sudo.
- – sftpuser1 – User will only have SFTP access to the server and can upload and download files from their respective sftp sub-folders.
- – sftpuser2 – User will only have SFTP access and can upload and download files from their respective sftp sub-folders.
adduser sftpadminusermod -a -G sftp-admin sftpadminadduser sftpuser1adduser sftpuser2
Configure the SSH keys for authentication for each of the new SFTP user accounts:
sudo su – sftpuser1ssh-keygencd .sshmv id_rsa.pub authorized_keyschmod u+rw-x,g-rwx,o-rwx authorized_keys# Copy the private key located in the id_rsa file and store it in a protected# location. It will be required for accessing the server later.rm id_rsaexit
Repeat the above commands for sftpuser2.
Configure the /sbin/nologin shell for the SFTP users to restrict SSH access to the server:
usermod -s /sbin/nologin sftpuser1usermod -s /sbin/nologin sftpuser2
SFTP Folders Setup
A new SFTP folder and SFTP user sub-folders will need to be created to allow the correct permissions to be applied to allow admin users access to the SFTP user folders and restrict the SFTP users to only be able to access their own folders.
mkdir /sftpchgrp sftp-admin /sftpchmod u+rwx,g+rxs-w,o+rx-w /sftpcd /sftpmkdir sftpuser1cd sftpuser1mkdir download uploadchown sftpuser1 download uploadchmod u+rwx,g+rwxs,o-rwx download uploadcd ..mkdir sftpuser2cd sftpuser2mkdir download uploadchown sftpuser2 download uploadchmod u+rwx,g+rwxs,o-rwx download upload
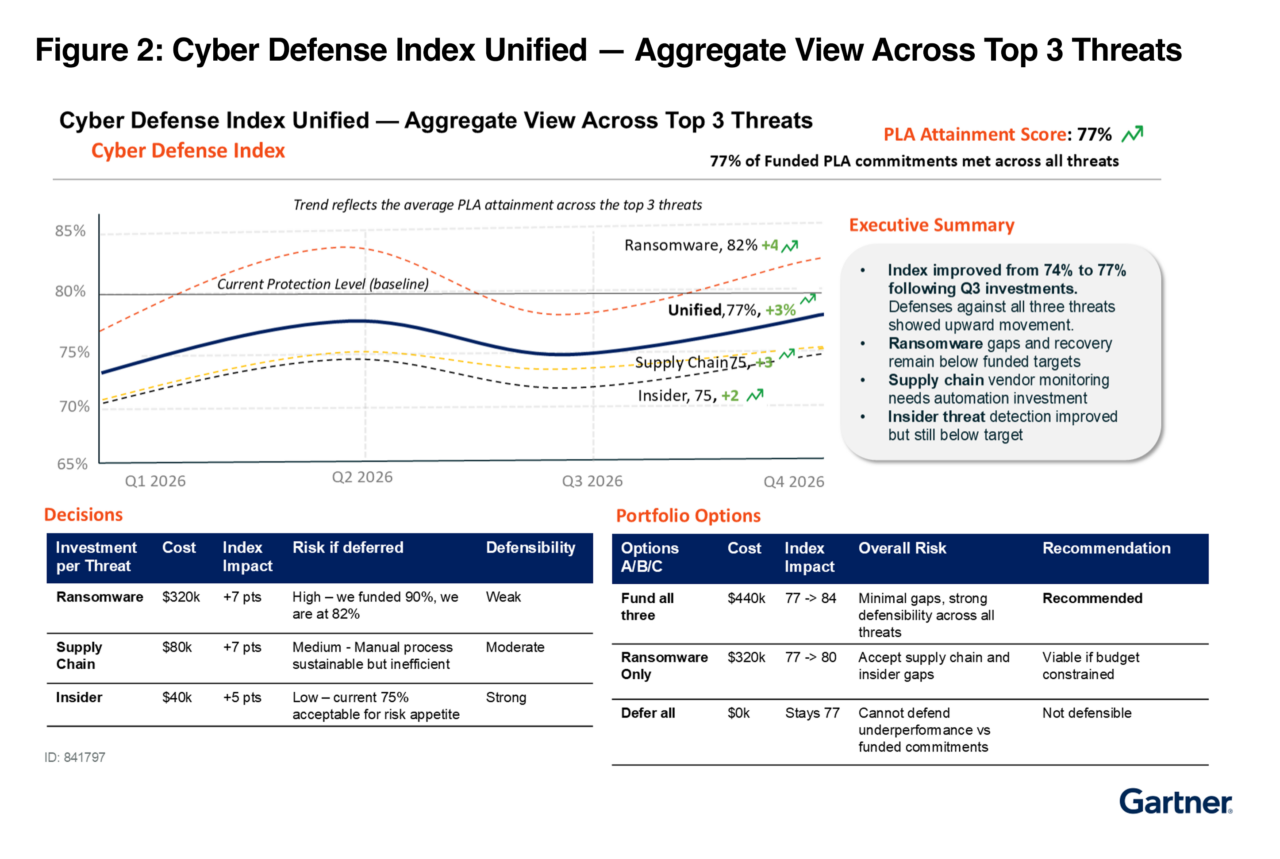
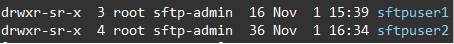
The /sftp folder must be owned by root and the group and other permissions both need read and execute permissions on the folder. Setting the group to sftp-admin provides the necessary permissions required for the sftpadmin user to be able to access the folder. Group permissions also include the setuid bit which will preserve the sftp-admin group on any sub-folders created in the sftp folder. The following image depicts the correct permissions and ownership required for the /sftp folder:
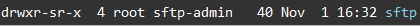
The SFTP user folder names (sftpuser1 and sftpuser2) need to match the usernames of the actual users. The folders need to also be owned by root with read and execute permissions for the group and others. The following image depicts the correct permissions and ownership required for the SFTP user folders:
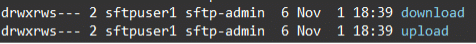
The download and upload folders need to be owned by the individual user that will be using the folders to provide them access to the folders. The group needs to be set to sftp-admin to provide access to the sftpadmin user. Both the user and group should have read, write, and execute permissions configured. The following image depicts the correct permissions and ownership required for the sftpuser1 download and upload folders:
SSHD Configuration
SSHD will need to be configured to restrict which users can SSH into the server vs. the users you only want using SFTP.
# backup the existing ssh_config filecp /etc/ssh/ssh_config /etc/ssh/ssh_config.originalvi /etc/ssh/ssh_config
Comment out the following line because we will be using the internal-sftp subsystem:
Subsystem sftp /usr/libexec/openssh/sftp-server
Add the following at the end of the configuration file:
Subsystem sftp internal-sftp
# Force all users except the ec2-user to use SFTP
Match User *,!ec2-user
ChrootDirectory /sftp/%uForceCommand internal-sftp -u 0002X11Forwarding noAllowTcpForwarding no
The above configuration forces all users to only be able to use SFTP except the “ec2-user.” The “ec2-user” will be able to use SSH and SFTP. When using SFTP, the ec2-user will start in their home folder (/home/ec2-user) and all other users will be restricted to /sftp/ folder and sub-folders. The following is a breakdown of each configuration line:
- – “Subsystem sftp internal-sftp” specifies to use the SFTP process that is built-in to the SSH daemon and simplifies using the ChrootDirectory directive since it doesn’t require any additional support files.
- – “Match User *,!ec2-user” will match all users except “ec2-user” and use the indented directives specified after the match line.
- – “ChrootDirectory /sftp/%u” will restrict all SFTP users to the /sftp/ folder and sub-folders.
- – “ForceCommand internal-sftp -u 0002” forces the use of the built-in SFTP process and configures the umask to 0002 during the SFTP session.
- – “X11Forwarding no” line prevents SFTP users from forwarding X sessions.
- – “AllowTcpForwarding no” line prevents SFTP users from forwarding TCP ports.
Restart the SSH daemon to use the new configuration:
systemctl restart sshd
Testing
Create some test files in the SFTP user’s download folders:
sudo su – sftpadmincd /sftp/sftpuser1/downloadtouch user1-test1.txt user1-test2.txt user1-test3.txtcd /sftp/sftpuser2/downloadtouch user2-test1.txt user2-test2.txt user2-test3.txt
All the following tests should pass successfully:
- Verify the ec2-user can open an SSH session to the server.
- Verify the ec2-user can open an SFTP session and is placed in the /home/ec2-user folder.
- Verify the sftpuser1 and sftpuser2 users cannot open an SSH session successfully.
- Verify the sftpuser1 and sftpuser2 users can open an SFTP session.
- Verify the sftpuser1 and sftpuser2 users only have access to the upload and download folders and can’t navigate anywhere else on the filesystem.
- Verify the sftpuser1 user sees the user1-*.txt files in the download folder and can successfully download and delete the files.
- Verify the sftpuser2 user sees the user2-*.txt files in the download folder and can successfully download and delete the files.
- Verify the sftpuser1 and sftpuser2 users can upload some test files into the upload folder.
- Verify the sftpadmin user can access the files in the SFTP user’s upload folders and delete the files.
You now have successfully configured SFTP to restrict who can access the server using SSH and/or SFTP. Users that are restricted to SFTP-only access are limited to which folders they can access on the server, eliminating the possibility of someone accessing system files or other files. Users associated with the sftp-admin group can access any files uploaded by the SFTP users, eliminating the need to have root privileges to access the files. Any new users added to the server won’t have SSH or SFTP access by default unless they are set up and configured correctly.
Contact us for more help on restricting SFTP access!