InfoSec App on Splunk Cloud – Part 1: Installing and Configuring
By: Khristian Pena | Team Lead
Are you looking to introduce security use cases to your Splunk Cloud deployment? If so, there’s a free app that is your entry to continuous monitoring and security investigations. The InfoSec App on Splunk is an entry level security solution powered by the Splunk platform that is designed to address the most common security use cases. You can also leverage the InfoSec app for a variety of advanced threat detection use cases and expand them using other security apps and add-ons that you can download from Splunkbase.
The following free Add-ons must be installed before you can start using InfoSec App on Splunk:
• Splunk Common Information Model (CIM): https://splunkbase.splunk.com/app/1621/
• Punchcard visualization: https://splunkbase.splunk.com/app/3129/
• Force Directed visualization: https://splunkbase.splunk.com/app/3767/(use add-on version 3.0.1 in Splunk Cloud)
• Lookup File Editor: https://splunkbase.splunk.com/app/1724/(new requirement starting from InfoSec v1.5)
• Sankey Diagram visualization: https://splunkbase.splunk.com/app/3112/(a new optional prerequisite for the experimental VPN Access dashboard starting from v1.5.3)
InfoSec App – https://splunkbase.splunk.com/app/4240/#/details
How to install apps & add-ons for the InfoSec App on Splunk Cloud
From your home screen you can download and install apps & add-ons by selecting the gear icon on the left side of the screen above your list of apps.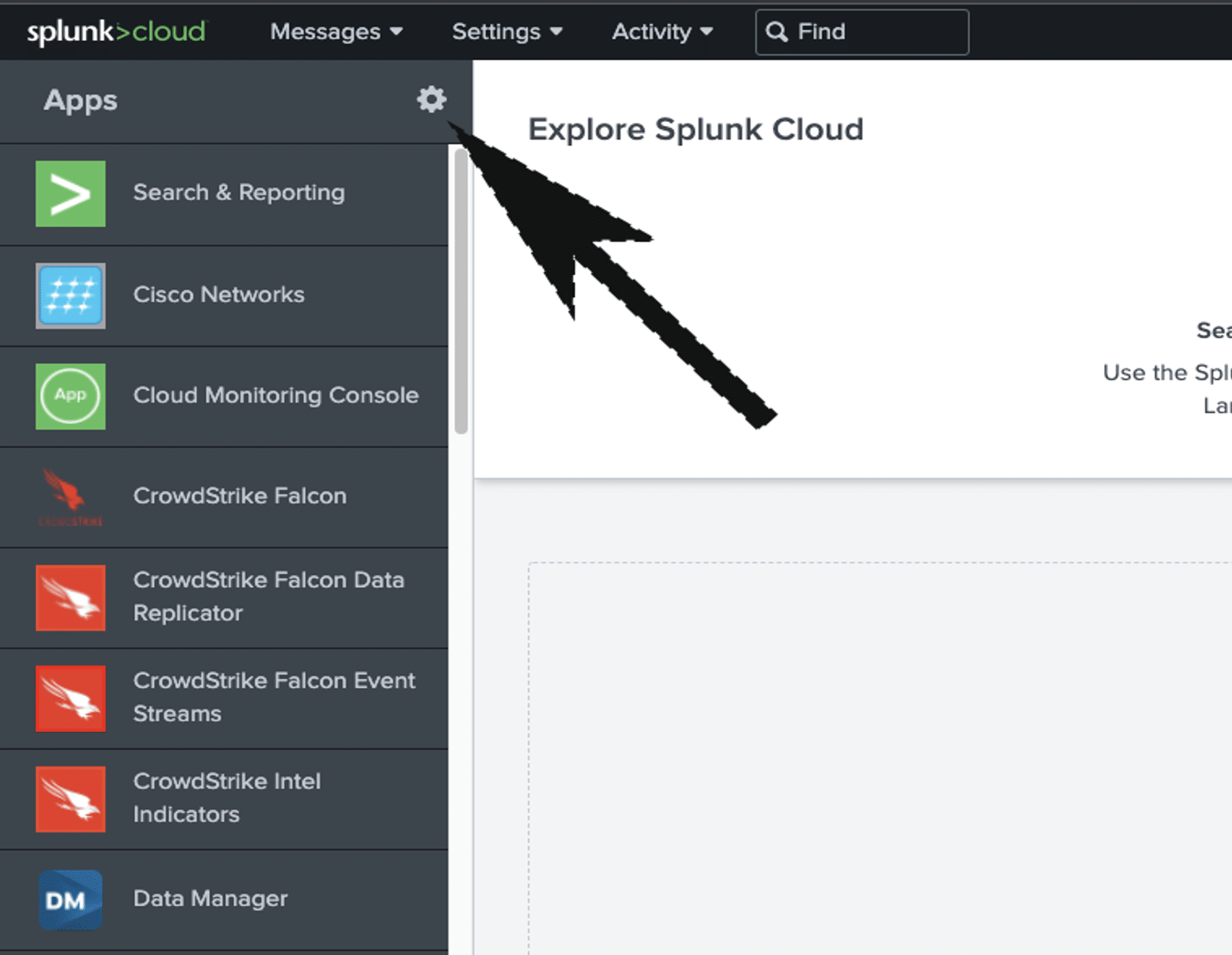
- You can access public apps from Splunkbase by selecting the Browse more apps option on the following screen.
- Find your app or add-on, then click Install
- Enter your Splunk.com login credentials and select the checkbox to accept the app license terms
- Select Login and Install
a. The app/add-on is downloaded from Splunkbase and installed on your deployment.
Note. You can install most Splunk apps on Splunk Cloud in a self-service manner without assistance from Splunk support except for customers that are on a Classic Cloud Experience designation. To determine your Splunk Cloud platform Experience select Support & Services > About located on the top right hand corner of your Splunk Cloud Web. In the About panel, under Splunk Cloud you will find your experience (Classic or Victoria).
Data Requirements & Prerequisites
The following Data Models must contain data and be accelerated (examples included):
Splunk Overview of Data Models and Acceleration:
https://docs.splunk.com/Documentation/SplunkCloud/8.2.2202/Knowledge/Aboutdatamodels
• Authentication
-
- Active Directory Data from the Windows Logs on Domain Controllers or O365
- Linux Auth Logs
- Cloud (AWS, Azure, or GCP) Authentication Data
- Okta
- Duo
- Cisco ISE
• Change
-
- Windows Event Logging
- S3 Audit Logs
- ServiceNow
- Puppet
• Intrusion Detection
-
- Palo Alto Networks
- Cisco FirePOWER
- Check Point
• Malware
-
- Crowdstrike
- Symantec
- McAfee
- Trend Micro
- Sophos
• Network_Sessions
-
- Zscaler
- Palo Alto Networks
- Cisco ASA
- AWS VPC Flow
- Cisco iOS
- Juniper
- Netflow
• Network_Traffic
-
- Palo Alto
- Zscaler
- SolarWinds
• Endpoint
-
- Crowdstrike Falcon Insight
- Microsoft Endpoint Manager
- Cisco Anyconnect
• Web
-
- IIS
- Fortinet
- WebSense
- Apache
All data used by InfoSec app must be Common Information Model (CIM)- compliant. The easiest way to accomplish this is by using CIM-compliant data and the appropriate add-ons that will normalize and tag your data appropriately. There are custom solutions that require tagging and event types when your data is not being mapped to the data models but that will not be covered in this guide.
This concludes part 1 of Installing and Configuring InfoSec app on Splunk Cloud. Part 2 will be released soon and will contain additional information about leveraging the app and the dashboards, reports, and alerts available. It will also include basic troubleshooting tips and best practices when utilizing the app.
Want to learn more about introducing security use cases to your Splunk Cloud deployment?
Contact us today!